The Common Vulnerabilities and Exposures (CVE) system identifies all vulnerabilities and threats related to the security of information systems. This system provides a reference-method for publicly known information-security vulnerabilities and exposures. The catalog is sponsored by the United States Department of Homeland Security (DHS). This system was officially launched for the public in September 1999.
The CVE glossary uses Security Content Automation Protocol (SCAP) to collect information about security vulnerabilities. In fact, SCAP uses CVE, and CVE IDs are listed on MITRE’s system as well as in the US National Vulnerability Database.

In CVE, threats are divided into two categories: vulnerabilities and exposures.
- Vulnerability: It is a mistake in software that can be directly used by a hacker to gain access to a system or network.
- Exposure: it is a mistake that gives an attacker indirect access to a system or network. It could allow an attacker to gather customer information that could be sold. In other words, an information security exposure is a mistake in software that allows access to information or capabilities that can be used by a hacker as a stepping-stone into a system or network.
The CVE assigns a unique identifier to each vulnerability.
CVE Identifiers (also called “CVE names,” “CVE numbers,” “CVE-IDs,” and “CVEs”) are unique, common identifiers for publicly known information security vulnerabilities. CVE identifier is as follow:
CVE-YYYY-NNNN
- YYYY is the year of publication
- NNNN a unique identifier number
So, each CVE Identifier includes the following:
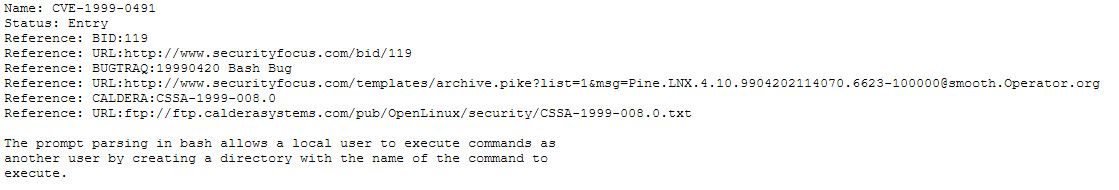
- CVE identifier number (i.e., “CVE-1999-0187”): CVE numbers are given to each new CVE issue by MITRE. However, it is worthwhile noting that MITRE is not the only one. As of December 2018, 93 commercial entities are authorized to act as CVE Numbering Authorities (CNA), including Adobe, Apple, Cisco, Linux, Google, HP, IBM, Microsoft, Mozilla, Oracle, and Red Hat.
- Indication of “entry” or “candidate” status. CVE identifiers had a status of “candidate” (“CAN-“) and could then be promoted to entries (“CVE-“), however this practice was ended some time ago and all identifiers are now assigned as CVEs.
- Brief description of the security vulnerability or exposure.
- Any pertinent references (i.e., vulnerability reports and advisories or OVAL-ID).
CVE Identifiers are used by information security product/service vendors and researchers as a standard method for identifying vulnerabilities and for cross-linking with other repositories that also use CVE Identifiers.
CVEs are assigned by a CVE Numbering Authority (CNA); there are three primary types of CVE number assignments:
- The Mitre Corporation functions as Editor and Primary CNA
- Various CNAs assign CVE numbers for their own products (e.g. Microsoft, Oracle, HP, Red Hat, etc.)
- A third-party coordinator such as CERT Coordination Center may assign CVE numbers for products not covered by other CNAs.

The CVE only concern software. When a flaw is detected, it is called a “0 Day”. This means that it has not been published or corrected. If the target company accepts the flaw, it can ask the MITRE to validate the CVE. If MITRE considerates that the software in question is widely used and supported it will validate the request of the company. It is also entitled to refuse. When the MITRE gives its consent, it provides a unique CVE identifier to the company which must in turn fill a form with a full description of the flaw.
The two companies that publish the most CVE are Apple and Microsoft. For a company, publish a CVE is synonymous with transparency with consumers regarding their security policy.
Source: httpcs.com

A CVE listing only contains the standard identifier number with status indicator, a brief description and references to related vulnerability reports and advisories. The US National Vulnerability Database (NVD) does include fix, scoring, and other information for identifiers on the CVE List. According to CVE, the goal of the program is to be “comprehensive.” Estimates of what percentage are missing from the list range from about a third to nearly half.
You can see one of the items in a list as an example:

Each CVE receives a CVSS score from the NVD, indicating its security severity. The CVSS score follows a formula made up of several security metrics. These metrics are:
- Its access vector
- The attack complexity
- The confidentiality of data processed by the system containing the vulnerability
- The integrity of the exploited system

New CVE Identifiers are added to the CVE website daily basis and are immediately available. The latest version of the CVE is on the CVE List Master Copy page. A free tool from CERIAS/Purdue University monitors changes to the CVE List.
————–
Sources: