Wireless Networks Security
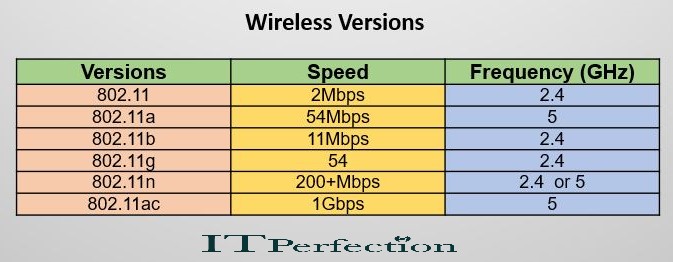
IEEE proposed the 802.11 standards for wireless communications. Various versions have been developed in wireless networking hardware:
WLAN Security Techniques and Protocols
Security techniques and protocols for wireless communication include:
- Service Set Identifier (SSID): It is a name that identifies a wireless network. Each wireless network must have a SSID. Security provided by an SSID is low because most Access Points broadcast their SSID and the SSID can be easily sniffed.
- Wired Equivalent Privacy (WEP): It was originally conceived as a security protocol to provide the same level of confidentiality that wired networks have. WEP uses either a 40-bit or 104-bit key to form a 64-bit or 128-bit key. WEP keys can be easily cracked by readily available software in a matter of minutes. WEP supports two methods of authentication: 1- OSA 2- SKA
- Wi-Fi Protected Access (WPA and WPA2): They were created to solve WEP’s problems, and have stronger security. WPA uses the Temporal Key Integrity Protocol TKIP to address some of the encryption problems in WEP. Also, WPA and WPA2 support various EAP extensions to enhance WLAN security.
Open System Authentication (OSA): In OSA mechanism, first, the computer sends a request for authentication to the access point. Then the access point generates an authentication code (for use only during that session). Finally, the computer accepts the authentication code and becomes part of the network as long as the session continues and the computer remains within range of the original access point.
Shared Key Authentication (SKA): It pre-establishes that a requesting system has knowledge of a shared secret key required for authentication. For exchange encrypted data between a WEP network access point and a wireless-equipped computer, SKA is required, because SKA is stronger than OSA in encryption.
Temporal Key Integrity Protocol (TKIP): It combines a secret root key with the initialization vector by using a key-mixing function. TKIP is based on the RC4 cipher, rather than the (assumed) more secure AES. The key used for encryption in TKIP is 128 bits long. WPA that uses TKIP is considered unreliable still.
Extensible Authentication Protocol (EAP): It is an authentication framework. The EAP protocol can support multiple authentication mechanisms. EAP runs directly over the link layer without requiring IP.
EAP is a lock step protocol which only supports a single packet in at a time. As a result, it cannot efficiently transport bulk data.
