Operate and Maintain Detective and Preventative Measures
These days, one of the most important aspects of cyber security is operate and maintain detective and also preventative measures. In this part of this tutorial, we’ll take a look at operate and maintain detective and also preventative measures to help you understand the different aspects of these operates. We discuss about the operating and maintaining security systems to prevent or minimize attacks on a network, in this section. There are some Detective and preventive security measures that those include various security technologies and techniques:
- Firewalls
- IDSs & IPSs
- Whitelisting and Blacklisting
- Sandboxing
- Honeypots and Honeynets
- Anti-malware
Firewalls
Firewall treat as a common tool in many security toolkits. There are two types of firewalls: software firewalls and hardware firewalls. When it comes to security concept, firewall are the first thing that comes to mind.
Firewall determines which packet is allowed to move on network traffic? What data packet allowed be entered into a computer? What packet should be drop? Which ports should be open? Which input / output packets should be encrypted? In general, it determines the do’s and don’ts of different network traffic.
Firewalls are usually deployed at the network or data center perimeter and at other network boundaries, such as between zones of trust.
Firewall configuration is not a sufficient condition for network security, but it is a necessary condition. In fact, just setting up a firewall does not make the network secure, but a network without a firewall is certainly not secure.
From a firewall point of view, network data is divided into two categories. The package that the computer receives from the network (Inbound) and the package that the computer sends to the network (Outbound).
It should be clearly defined the subset of risks that are appropriately mitigated by firewalls. Firewalls operate by enforcing rules, and those rules are mostly static.
When a firewall receives a packet, it first detects the type of packet. It then goes on to list his own rules. If there is a rule for this packet, then immediately the rule applies, but if the rule is not defined for this packet:
- If the packet is part of the inbound traffic, then the firewall will drop the above packet.
- If the packet is part of the outbound traffic, then the firewall will allow the above packet to move and will consider it as part of the allowed traffic.
The operational challenge is to both accurately track the current sets of rules and have a process to identify rules that must be added, modified, or deleted.
Today, increasingly, host-based firewalls are being deployed to protect endpoints and virtual servers throughout the data center.
Intrusion Detection and Prevention Systems
An Intrusion Detection System (IDS) is a detective device designed to detect malicious including policy-violating actions. Also, an Intrusion Prevention System (IPS) is a preventive device designed to prevent malicious actions.
IDS and IPS are discussed earlier in communication and network security domain. Also we discussed again about IDS and IPS, in this domain and in “Conduct Logging and Monitoring Activities” section.
Anyway, as we said earlier in “Conduct Logging and Monitoring Activities” section, there are two basic types of IDSs and IPSs: Network-based (NIDS and NIPS) and Host-based (HIDS and HIPS).
Today some networks use a combination of NIDS and NIPS.
A NIDS is passive device that detects malicious traffic on a network. NIDS often require promiscuous network access to analyze all traffic, including all unicast traffic.
The NIPS (unlike NIDS) alters the flow of network traffic. And that’s the difference between NIDS and NIPS. The NIPS often has a smaller set of rules compared to a NIDS.
There are two types of NIPS:
- Active response: It may kill malicious traffic through a variety of methods.
- Inline: An inline NIPS is “in line” with traffic, playing the role of a firewall by passing or allowing traffic.
NIPS also provides defense-in-depth protection.
And finally, HIDS and HIPS process network traffic as it enters the host.
Whitelisting and Blacklisting
One of the most effective measures to protect computers and the entire network, is to separate all common functions as well as all available applications in two separate lists. Put your trusted actions and plans (such as email delivery from a known sender, traffic from a specific IP address range, or execution of a trusted application) on the whitelist and everything else on the blacklist.
Whitelisting involves explicitly allowing some action. Blacklisting explicitly blocks specific actions.
This is an effective preventative measure that prevents users from running unauthorized applications or send/receive emails with unreliable/unauthorized people.
Whitelisting and blacklisting can be automated. They can also help prevent malware infections.
Third-Party Provided Security Services
There are a variety of third-party security services. For example auditing, SIEM, penetration testing, or forensic services. Third-party security services cover a wide spectrum of possible security services.
Sandboxing
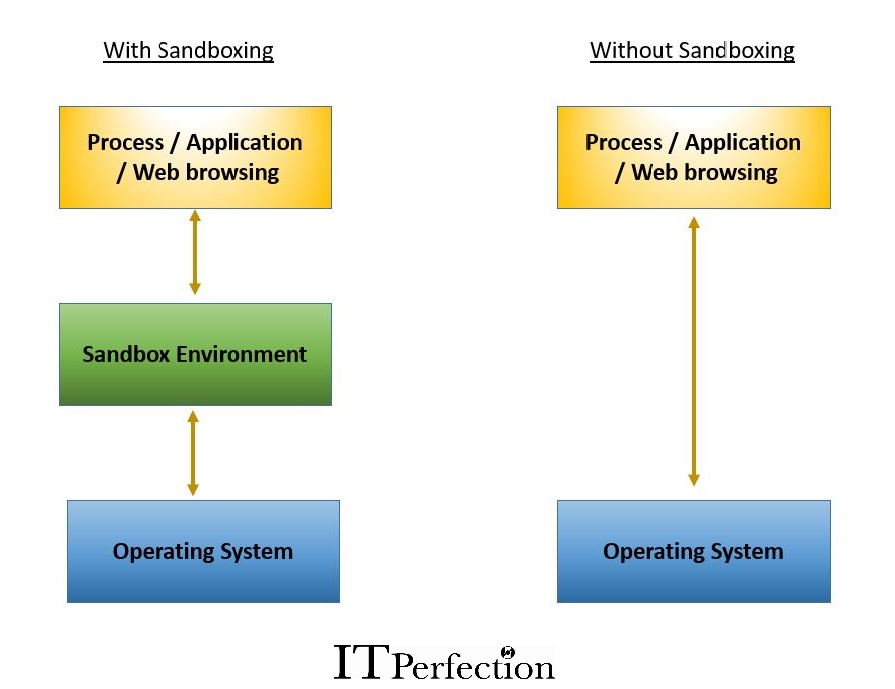
A sandbox enables untrusted or unknown programs to be executed in a separate, isolated operating environment. In other words, a sandbox is an application execution environment that isolates the executing code from the operating system to prevent security violations.
When we sandbox an application, it behaves as if it were communicating directly with the OS.
Sandboxing is used in many types of systems today, including anti-malware, web filtering, and intrusion prevention systems (IPS).
Honeypots and Honeynets
Honeypots: individual computers, network computers, folders, or files created as a trap for intruders.
Honeynet: two or more networked honeypots used together to simulate a network.
Administrators usually configure honeypots with vulnerabilities to lure intruders into attacking them. They may be unpatched or have security vulnerabilities that administrators purposely leave open.
The goal is to grab the attention of intruders and keep the intruders away from the legitimate network that is hosting valuable resources.
Another benefit is that after the attacker’s attention is drawn and something is done, the attacker’s approach as well as his behavior can be monitored and analyzed. Identifying malware behavior is very important today and allows us to better identify and fix security vulnerabilities in our systems.
Anti-malware
Anti-malware (also known as antivirus) is a software that designed to detect and deactivate malicious software, including viruses, worms, and Trojan horses.
The anti-malware software compares the contents of the file being opened or stored against a database of malware signatures. If a malware signature is matched, then anti-malware software prevents the file from being opened or saved. Of course, anti-malware also alerts the user.
The most important protection against malicious code is the use of anti-malware software with up-to-date signature files.
Advanced anti-malware tools use various advanced techniques such as machine learning to detect and block malware from executing on a system.
There are two general categories of anti-malware software:
- For personal computers (often called Desktop)
- For the network and its computers (sometimes called Enterprise)
Anti-malware for personal computers, like any software, can be easily installed on a computer.
Networked anti-malware usually has two or three components:
- Management console (installed on malware server. this computer usually called Administration Server)
- Network Agent (which should be installed on all computers)
- Anti-malware software (which must be installed on all computers)
The connection between the anti-malware software of each computer and the management console is done through the network agent. Of course, some malware manufacturers sometimes, merge the second and third components and distribute them as only a software on computers.
When Enterprise anti-malware software find a malware (or even if it gives the possibility of malware in a file) , sends an alert to central management console so that the organization’s security team is alerted and can take the appropriate action.
Anti-malware software that has an old database will not detect the existence of many malware. So it is very important that the database of these softwares is always up to date.
